In my last 2 blog post I covered the creation of group policy objects for distributing certificates to all computers in a domain and enable Network Level Authentication on them plus also covered how to create and use WMI filters to specify which machines a Group Policy Object should apply to. On this blog post I will cover how to do this with Windows 2008 R2 built in PowerShell Module and some external ones from SDM Software. The GPO that we will be creating is to disable RDP on none Vista, Windows 7 and Windows 2008 hosts since following the other blog posts these do not support NLA on their Remote Desktop Service. We will use PowerShell on a Windows 2008 R2 Domain Controller. Since we are going to use external scripts we would first start modifying the execution policy this is done by running the Set-ExecutionPolicy command to allow local scripts to execute without the need of being signed.
PS C:\Windows\system32> Set-ExecutionPolicy remotesigned
Execution Policy Change
The execution policy helps protect you from scripts that you do not trust. Changing the execution policy might expose
you to the security risks described in the about_Execution_Policies help topic. Do you want to change the execution
policy?
[Y] Yes [N] No [S] Suspend [?] Help (default is "Y"): y
PS C:\Windows\system32>
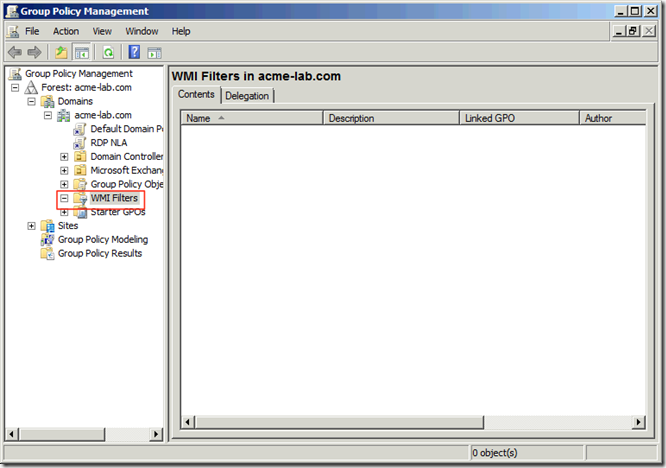
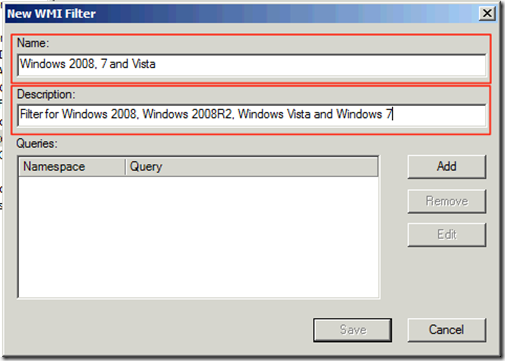
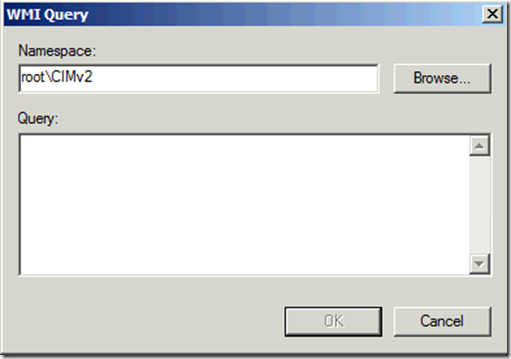
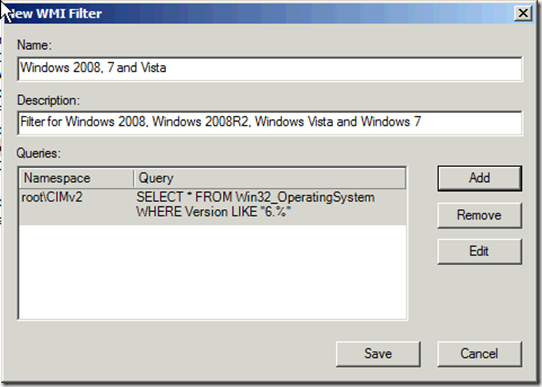
As stated by the command this could be a potential security risk so do remember to re-run the command at the en with the execution policy of Restricted. Before we start creating group policy objects and linking them we should create a WMI Filter that we will attach to the policy. I took the liberty to write one based on another one I saw in the Microsoft Scripting Repository that will create a series of base filters for you when ran in a Domain Controller running Windows 2008 or Windows 2008 R2. You can download the script from my GitHub account at https://github.com/darkoperator/powershell_scripts/blob/master/create-wmifilters.ps1 the script will make the necessary changes to the registry to allow modification of attributes locally on the box thus allowing us to add the filters. The script is ran from a PoweShell Window providing the path like any other PowerShell script:
PS C:\Users\Administrator\Documents> .\create-wmifilters.ps1
Checking is registry key is set to allow changes to AD System Only Attributes is set.
Allow System Only Change key is not set
Creating key and setting value to 1
Starting creation of WMI Filters:
Adding WMI Filter for: Virtual Machines
Adding WMI Filter for: Workstation 32-bit
Adding WMI Filter for: Workstation 64-bit
Adding WMI Filter for: Workstations
Adding WMI Filter for: Domain Controllers
Adding WMI Filter for: Servers
Adding WMI Filter for: Windows 2000
Adding WMI Filter for: Windows XP
Adding WMI Filter for: Windows Vista
Adding WMI Filter for: Windows 7
Adding WMI Filter for: Windows Server 2003
Adding WMI Filter for: Windows Server 2008
Adding WMI Filter for: Windows Server 2008 R2
Adding WMI Filter for: Windows Vista and Windows Server 2008
Adding WMI Filter for: Windows Server 2003 and Windows Server 2008
Adding WMI Filter for: Windows 2000, XP and 2003
Finished adding WMI Filters
Disabling Allow System Only Change Attributes on server
Now you will have some WMI Filters we can use as base in our Group Policy Objects, do remember that we can have several filters linked to a single GPO.
Once this is done we can import the GroupPolicy PowerShell module that is installed on Windows 2008 Domain Controllers when promoted and look at the available commands we get from the module:
PS C:\> Import-Module grouppolicy
PS C:\> Get-Command -Module grouppolicy | Format-Table -AutoSize
CommandType Name Definition
----------- ---- ----------
Cmdlet Backup-GPO Backup-GPO -Guid <Guid> -Path <String> [-Comment <String>] [-Domain <String>]...
Cmdlet Copy-GPO Copy-GPO -SourceGuid <Guid> -TargetName <String> [-SourceDomain <String>] [-T...
Cmdlet Get-GPInheritance Get-GPInheritance [-Target] <String> [-Domain <String>] [-Server <String>] [-...
Cmdlet Get-GPO Get-GPO [-Guid] <Guid> [[-Domain] <String>] [[-Server] <String>] [-All] [-Ver...
Cmdlet Get-GPOReport Get-GPOReport [-Guid] <Guid> [-ReportType] <ReportType> [[-Path] <String>] [[...
Cmdlet Get-GPPermissions Get-GPPermissions -Guid <Guid> [-TargetName <String>] [-TargetType <Permissio...
Cmdlet Get-GPPrefRegistryValue Get-GPPrefRegistryValue -Guid <Guid> -Context <GpoConfiguration> -Key <String...
Cmdlet Get-GPRegistryValue Get-GPRegistryValue -Guid <Guid> -Key <String> [-ValueName <String>] [-Domain...
Cmdlet Get-GPResultantSetOfPolicy Get-GPResultantSetOfPolicy [-Computer <String>] [-User <String>] -ReportType ...
Cmdlet Get-GPStarterGPO Get-GPStarterGPO -Guid <Guid> [-Domain <String>] [-Server <String>] [-All] [-...
Cmdlet Import-GPO Import-GPO -BackupId <Guid> -Path <String> [-TargetGuid <Guid>] [-TargetName ...
Cmdlet New-GPLink New-GPLink -Guid <Guid> -Target <String> [-LinkEnabled <EnableLink>] [-Order ...
Cmdlet New-GPO New-GPO [-Name] <String> [-Comment <String>] [-Domain <String>] [-Server <Str...
Cmdlet New-GPStarterGPO New-GPStarterGPO [-Name] <String> [-Comment <String>] [-Domain <String>] [-Se...
Cmdlet Remove-GPLink Remove-GPLink -Guid <Guid> -Target <String> [-Domain <String>] [-Server <Stri...
Cmdlet Remove-GPO Remove-GPO -Guid <Guid> [-Domain <String>] [-Server <String>] [-KeepLinks] [-...
Cmdlet Remove-GPPrefRegistryValue Remove-GPPrefRegistryValue [[-Server] <String>] -Guid <Guid> -Context <GpoCon...
Cmdlet Remove-GPRegistryValue Remove-GPRegistryValue [-Guid] <Guid> [-Key] <String> [[-ValueName] <String>]...
Cmdlet Rename-GPO Rename-GPO -Guid <Guid> -TargetName <String> [-Domain <String>] [-Server <Str...
Cmdlet Restore-GPO Restore-GPO -BackupId <Guid> -Path <String> [-Domain <String>] [-Server <Stri...
Cmdlet Set-GPInheritance Set-GPInheritance [-Target] <String> -IsBlocked <BlockInheritance> [-Domain <...
Cmdlet Set-GPLink Set-GPLink -Guid <Guid> -Target <String> [-LinkEnabled <EnableLink>] [-Order ...
Cmdlet Set-GPPermissions Set-GPPermissions -Guid <Guid> -PermissionLevel <GPPermissionType> -TargetNam...
Cmdlet Set-GPPrefRegistryValue Set-GPPrefRegistryValue -Guid <Guid> -Context <GpoConfiguration> -Key <String...
Cmdlet Set-GPRegistryValue Set-GPRegistryValue -Guid <Guid> -Key <String> [-ValueName <String[]>] [-Valu...
We now use the New-GPO comandlet to create a new empty GPO named DisableRDP:
PS C:\> New-GPO -Name "DisableRDP"
DisplayName : DisableRDP
DomainName : acme-lab.com
Owner : ACME-LAB\Domain Admins
Id : 31122b47-5129-420f-9fe8-241584cc516d
GpoStatus : AllSettingsEnabled
Description :
CreationTime : 3/20/2012 7:56:43 AM
ModificationTime : 3/20/2012 7:56:44 AM
UserVersion : AD Version: 0, SysVol Version: 0
ComputerVersion : AD Version: 0, SysVol Version: 0
WmiFilter :
Now that we have a Group Policy Object created we can use the commadlet to create a registry reference in the GPO that will be applied to the machines that process the GPO under the context of Computer:
PS C:\> Set-GPPrefRegistryValue -Name DisableRDP -Key "HKLM\System\CurrentControlSet\Control\Terminal Server" -ValueName fDenyTSConnections -Value 1 -Type Dword -Context computer -Action update
Now to be able to link a WMI Filter to a GPO we need some external commands provided for free by SDM Software from http://www.sdmsoftware.com/products/freeware/ and we download the SDM GPMC PowerShell Cmdlets and install them on the Domain Controller. Once installed we can load the module:
PS C:\Users\Administrator\Documents> import-module SDM-GPMC
We want to use the Add-SDMWMIFilterLink command to link our GPO with one of the WMI Filters we created for the target of the GPO. To look at examples on how to use it we use the help command with the switch for examples:
PS C:\Users\Administrator\Documents> help Add-SDMWMIFilterLink -Examples
NAME
Add-SDMWMIFilterLink
SYNOPSIS
Adds a WMI Filter to a particular GPO
-------------- Example 1 --------------
C:\PS>Add-SDMWMIFilterLink "Wireless Policy" -FilterName "Laptop Test"
Links the WMI filter called "Laptop Test" to the GPO called "Wireless Policy"
Filter Laptop test linked to GPO Wireless Policy
As we can see the command is quite simple to use we just need to provide it a name for the GPO and a filter name to link to the GPO. Lets link now the GPO with the WMI Filter:
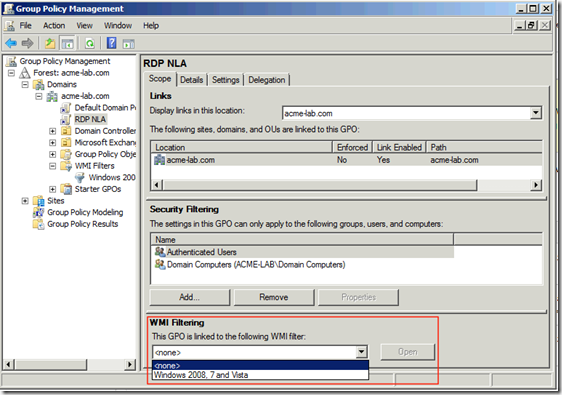
PS C:\Users\Administrator\Documents> Add-SDMWMIFilterLink "DisableRDP" -FilterName "Windows 2000, XP and 2003"
Filter Windows 2000, XP and 2003 linked to GPO DisableRDP
Once done we can now link the GPO to any part of our Active Directory structure. In this case I will attach it to the entire Forest of my lab AD infrastructure:
PS C:\Users\Administrator\Documents> New-GPLink -Name DisableRDP -Target "dc=acme-lab,dc=com”
GpoId : 31122b47-5129-420f-9fe8-241584cc516d
DisplayName : DisableRDP
Enabled : True
Enforced : False
Target : DC=acme-lab,DC=com
Order : 3
DisplayName : DisableRDP
DomainName : acme-lab.com
Owner : ACME-LAB\Domain Admins
Id : 31122b47-5129-420f-9fe8-241584cc516d
GpoStatus : AllSettingsEnabled
Description :
CreationTime : 3/20/2012 7:56:43 AM
ModificationTime : 3/20/2012 8:18:04 AM
UserVersion : AD Version: 0, SysVol Version: 0
ComputerVersion : AD Version: 1, SysVol Version: 1
WmiFilter :
DisplayName : DisableRDP
DomainName : acme-lab.com
Owner : ACME-LAB\Domain Admins
Id : 31122b47-5129-420f-9fe8-241584cc516d
GpoStatus : AllSettingsEnabled
Description :
CreationTime : 3/20/2012 7:56:43 AM
ModificationTime : 3/20/2012 7:56:44 AM
UserVersion : AD Version: 0, SysVol Version: 0
ComputerVersion : AD Version: 0, SysVol Version: 0
WmiFilter :
This could be a very good way to automate the process of creating Group Policy Objects in lab and then move this to a production environment. Also you could use it for automating disaster recovery procedures.
As always I hope you found this blog post useful and informative.