Using Posh-SecMod PowerShell Module to Automate Nessus (Part 3)
Listing Reports Available
We can retrieve a list of the reports available on the Nessus Server and the information that they provide with Get-NessusReports function and we provide it a index for the session or an object of Nessus.Server.Session :
C:\> Get-NessusReports -Index 0 ServerHost : 192.168.10.3 ReportID : a3fb5b8c-60db-1dda-fac7-ee46c0d0a638ea8ce79ab209483c ReportName : Dev Lab Full Scan Status : completed KB : True AuditTrail : True Date : 4/14/2013 2:36:21 AM Session : Nessus.Server.Session ServerHost : 192.168.10.3 ReportID : beb54ae5-ddd5-4700-3e85-d0241ade948354bf668ec4c5c319 ReportName : Lab Full Unauthenticated Scan Status : completed KB : True AuditTrail : True Date : 4/11/2013 6:39:22 AM Session : Nessus.Server.Session ServerHost : 192.168.10.3 ReportID : 908185a5-19cc-e2e4-6073-2134043611b99e3d5fcf060ec31e ReportName : Scan Dev Lab Status : completed KB : True AuditTrail : True Date : 4/11/2013 4:26:13 AM Session : Nessus.Server.Session ServerHost : 192.168.10.3 ReportID : 0c0a28e2-824a-3606-4bd2-965d0da1c62272dde8c29f1faa6d ReportName : Lab Scan 1 Status : completed KB : True AuditTrail : True Date : 4/14/2013 2:36:21 AM Session : Nessus.Server.Session
The main properties for each report object are:
- ReportID – This is the unique identifier of the report since Nessus Allows for several reports to have the same name. This is the value we will use for when requesting specific reports for their information.
- ReportName – The friendly name gave to the scan that generated the report.
- Status – When running a Nessus scan the information from the scan is populating a report as it is running so this property will tell us if the results are from a completed scan or is the scan still running.
- KB – this is know as the Knowledge Base of the scan and it is generated per host, this will tell you what plugins where launched and if any errors where encountered. If your Nessus server has less than 2GB of memory the KB is not generated for the hosts so as to save space in memory while executing. The information is stored in the server.
- AuditTrail – This is a execution information that is saved for each plugin it will tell us if the plugin ran with no issues and if a problem was found it will tell us what was the error message. This is saved per plugin and it is stored on the server.
- Date – This is the date when the report was launched in UTC .
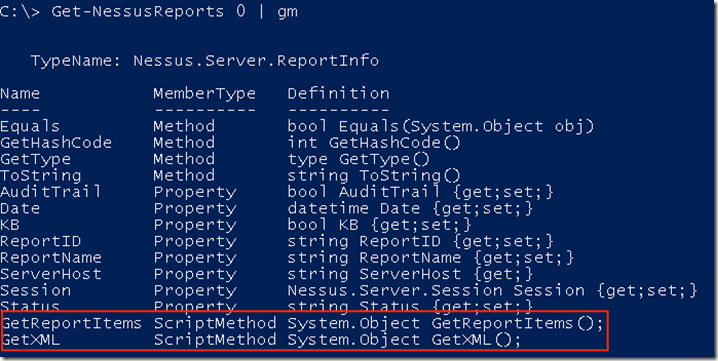
The Get-NessusReports function produces objects for each report and these have 2 ScriptMethods that we can use against the object it self
- GetReportItems() – this method retrieves al reported entries (Info, Low, Medium, High and Critical) with all the details for each in the properties of the object.
- GetXML() – This method retrieves the XML .Net object that represents the NessusV2 format of the report.
Getting a Summary of Each Host in a Report
We can query a report and get a summary of the hosts that are in the report and the number of items reported for each severity level, this is done with Get-NessusReportHostSummary.
C:\> Get-NessusReportHostSummary -Index 0 -ReportID a3fb5b8c-60db-1dda-fac7-ee46c0d0a638ea8ce79ab209483c Hostname : 192.168.10.10 Info : 51 Low : 1 Medium : 4 High : 0 Critical : 0 Hostname : 192.168.10.12 Info : 51 Low : 2 Medium : 5 High : 1 Critical : 1 Hostname : 192.168.10.13 Info : 95 Low : 2 Medium : 12 High : 0 Critical : 0 Hostname : 192.168.10.2 Info : 38 Low : 1 Medium : 1 High : 0 Critical : 0 Hostname : nessus.darkoperator.com Info : 39 Low : 1 Medium : 3 High : 0 Critical : 0
Getting a Summary per Vulnerability in a Report
We can get a summary for each item found and how many of them are in the report using the function Get-NessusReportVulnSummary
C:\> Get-NessusReportVulnSummary -Index 0 -ReportID a3fb5b8c-60db-1dda-fac7-ee46c0d0a638ea8ce79ab209483c
PluginID : 10107
PluginName : HTTP Server Type and Version
PluginFamily : Web Servers
Count : 5
Severity : Info
PluginID : 10147
PluginName : Nessus Server Detection
PluginFamily : Service detection
Count : 1
Severity : Info
PluginID : 10150
PluginName : Windows NetBIOS / SMB Remote Host Information Disclosure
PluginFamily : Windows
Count : 4
Severity : Info
PluginID : 10263
PluginName : SMTP Server Detection
PluginFamily : Service detection
Count : 2
Severity : Info
PluginID : 10267
PluginName : SSH Server Type and Version Information
PluginFamily : Service detection
Count : 1
Severity : Info
PluginID : 10287
PluginName : Traceroute Information
PluginFamily : General
Count : 4
Severity : Info
PluginID : 10394
PluginName : Microsoft Windows SMB Log In Possible
PluginFamily : Windows
Count : 3
Severity : Info
PluginID : 10736
PluginName : DCE Services Enumeration
PluginFamily : Windows
Count : 49
Severity : Info
PluginID : 10761
PluginName : COM+ Internet Services (CIS) Server Detection
PluginFamily : Windows
Count : 3
Severity : Info
PluginID : 10785
PluginName : Microsoft Windows SMB NativeLanManager Remote System Information
Disclosure
PluginFamily : Windows
Count : 4
Severity : Info
PluginID : 10863
PluginName : SSL Certificate Information
PluginFamily : General
Count : 5
Severity : Info
PluginID : 10881
PluginName : SSH Protocol Versions Supported
PluginFamily : General
Count : 1
Severity : Info
PluginID : 10884
PluginName : Network Time Protocol (NTP) Server Detection
PluginFamily : Service detection
Count : 2
Severity : Info
PluginID : 10940
PluginName : Windows Terminal Services Enabled
PluginFamily : Windows
Count : 4
Severity : Info
........
Getting all Host Information from a Report
If we want all the information available for each host in a report we use the function Get-NessusReportHostsDetailed, this function will download the report XML, Parse it and generate PowerShell objects for each piece of information found. The information will be divided in to 2 parts for each hosts
- Host_Properties – This is the information about the host that was gathered during the enumeration of the hosts including IP addresses, Netstat information, Operating System and other values.
- ReportItems – This are each of the entries in the vulnerabilities tab of a report.
C:\> Get-NessusReportHostsDetailed -Index 0 -ReportID a3fb5b8c-60db-1dda-fac7-ee46c0d0a638ea8ce79ab209483c
Host Host_Properties ReportItems
---- --------------- -----------
nessus.darkoperator.com @{system_type=general-purp... {@{Host=nessus.darkoperato...
192.168.10.2 @{operating_system=Microso... {@{Host=192.168.10.2; Port...
192.168.10.13 @{operating_system=Microso... {@{Host=192.168.10.13; Por...
192.168.10.12 @{operating_system=Microso... {@{Host=192.168.10.12; Por...
192.168.10.10 @{operating_system=Microso... {@{Host=192.168.10.10; Por...
Here is an example of the information we can get in the host properties:
C:\> $reporthost = Get-NessusReportHostsDetailed -Index 0 -ReportID a3fb5b8c-60db-1dda-fac7-ee46c0d0a638ea8ce79ab209483c | select -First 1
C:\> $reporthost.Host_Properties
system_type : general-purpose
netstat_listen_tcp4_0 : 0.0.0.0:22
local_checks_proto : local
netstat_listen_tcp46_3 : :::22
netstat_listen_tcp4_2 : 0.0.0.0:8834
HOST_START : Sun Apr 14 02:22:48 2013
host_ip : 192.168.10.3
operating_system : Linux Kernel 2.6.32-358.0.1.el6.x86_64 on CentOS release 6.4
(Final)
netstat_listen_tcp4_1 : 0.0.0.0:1241
mac_address : 00:0C:29:28:7A:F9
HOST_END : Sun Apr 14 02:31:13 2013
netstat_listen_tcp6_5 : :::8834
host_fqdn : nessus.darkoperator.com
netstat_listen_tcp6_4 : :::1241
Report items will contain the information about each vulnerability and each informational plugin that was lunched and was successful in executing.
C:\> $reporthost.ReportItems[3]
Host : nessus.darkoperator.com
Port : 0
ServiceName : general
Severity : Info
PluginID : 33276
PluginName : Enumerate MAC Addresses via SSH
PluginFamily : General
RiskFactor : None
Synopsis : This plugin enumerates MAC addresses on a remote host.
Description : By connecting to the remote host via SSH with the supplied
credentials, this plugin enumerates MAC addresses.
Solution : Disable any unused interfaces.
PluginOutput :
The following MAC address exists on the remote host :
- 00:0C:29:28:7A:F9 (interface eth0)
SeeAlso :
CVE :
BID :
ExternaReference :
PatchPublicationDate :
VulnPublicationDate :
Exploitability :
ExploitAvailable :
CANVAS :
Metasploit :
COREImpact :
MetasploitModule :
CANVASPackage :
CVSSVector :
CVSSBase :
CVSSTemporal :
PluginType : local
PluginVersion :
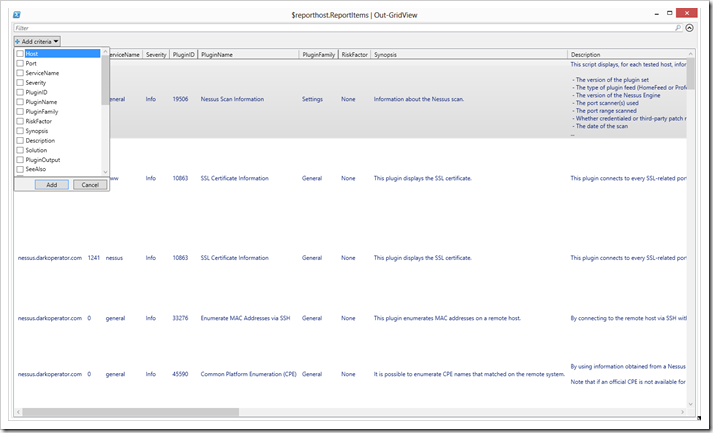
One of the great advantages of PowerShell is that it makes managing the large amount of data quite simple and provides options to export the objects in to XML, CSV and even generate our custom HTML reports. Lets look at the GridView option that allow us to see all the report items in a grid and even add filters to the view The command we use is:
$reporthost.ReportItems | Out-GridView
Working with the Nessus v2 XML
We can retrieve the XML .Net Object representation of a report if you which to manipulate the XML it self or use it for other purposes. Getting a XML .Net Object of the report and saving it to disk as a .nessus file
C:\> $nessusreport = Get-NessusV2ReportXML -Index 0 -ReportID a3fb5b8c-60db-1dda-fac7-ee46c0d0a638ea8ce79ab209483c
C:\> $nessusreport.Save("$env:HOMEPATH\Desktop\DevLabRepor.nessus")
Getting access to the information in XML is super easy since in PowerShell it is just like working with a regular .Net object
C:\> $nessusreport.NessusClientData_v2.Report.ReportHost
name HostProperties ReportItem
---- -------------- ----------
nessus.darkoperator.com HostProperties {ReportItem, ReportItem, R...
192.168.10.2 HostProperties {ReportItem, ReportItem, R...
192.168.10.13 HostProperties {ReportItem, ReportItem, R...
192.168.10.12 HostProperties {ReportItem, ReportItem, R...
192.168.10.10 HostProperties {ReportItem, ReportItem, R...
C:\> $nessusreport.NessusClientData_v2.Policy
policyName : All Plugins with Full Scan
policy_comments :
Preferences : Preferences
FamilySelection : FamilySelection
IndividualPluginSelection : IndividualPluginSelection
Filtering Report Items
I know that many people are new to PowerShell and still learning the power it has to filter and manipulate objects so the function Retrieve and filter report items Get-NessusReportItems is here to help with some of the filtering. The function will filter at the server the reported items for Host and Severity and return the appropriate report item objects for use:
C:\> Get-NessusReportItems -Index 0 -ReportID a3fb5b8c-60db-1dda-fac7-ee46c0d0a638ea8ce7b209483c -HostFilter 192.168.10.12 -SeverityFilter critical,high
Host : 192.168.10.12
Port : 3389
ServiceName : msrdp
Severity : High
PluginID : 58435
PluginName : MS12-020: Vulnerabilities in Remote Desktop Could Allow Remote
Code Execution (2671387) (uncredentialed check)
PluginFamily : Windows
RiskFactor : High
Synopsis : The remote Windows host could allow arbitrary code execution.
Description : An arbitrary remote code vulnerability exists in the
implementation of the Remote Desktop Protocol (RDP) on the remote
Windows host. The vulnerability is due to the way that RDP
accesses an object in memory that has been improperly initialized
or has been deleted.
If RDP has been enabled on the affected system, an
unauthenticated, remote attacker could leverage this
vulnerability to cause the system to execute arbitrary code by
sending a sequence of specially crafted RDP packets to it.
This plugin also checks for a denial of service vulnerability in
Microsoft Terminal Server.
Note that this script does not detect the vulnerability if the
'Allow connections only from computers running Remote Desktop
with Network Level Authentication' setting is enabled or the
security layer is set to 'SSL (TLS 1.0)' on the remote host.
Solution : Microsoft has released a set of patches for Windows XP, 2003,
Vista, 2008, 7, and 2008 R2 :
http://technet.microsoft.com/en-us/security/bulletin/ms12-020
PluginOutput :
SeeAlso :
CVE : {CVE-2012-0002, CVE-2012-0152}
BID : {52353, 52354}
ExternaReference : {OSVDB:80000, OSVDB:80004, EDB-ID:18606, IAVA:2012-A-0039...}
PatchPublicationDate : 2012/03/13
VulnPublicationDate : 2012/03/13
Exploitability : Exploits are available
ExploitAvailable : true
CANVAS : true
Metasploit : true
COREImpact : true
MetasploitModule : MS12-020 Microsoft Remote Desktop Checker
CANVASPackage : White_Phosphorus
CVSSVector : CVSS2#AV:N/AC:M/Au:N/C:C/I:C/A:C
CVSSBase : 9.3
CVSSTemporal : 7.3
PluginType : remote
PluginVersion :
Host : 192.168.10.12
Port : 5355
ServiceName : llmnr
Severity : Critical
PluginID : 53514
PluginName : MS11-030: Vulnerability in DNS Resolution Could Allow Remote Code
Execution (2509553) (remote check)
PluginFamily : Windows
RiskFactor : Critical
Synopsis : Arbitrary code can be executed on the remote host through the
installed Windows DNS client.
Description : A flaw in the way the installed Windows DNS client processes
Link- local Multicast Name Resolution (LLMNR) queries can be
exploited to execute arbitrary code in the context of the
NetworkService account.
Note that Windows XP and 2003 do not support LLMNR and successful
exploitation on those platforms requires local access and the
ability to run a special application. On Windows Vista, 2008, 7,
and 2008 R2, however, the issue can be exploited remotely.
Solution : Microsoft has released a set of patches for Windows XP, 2003,
Vista, 2008, 7, and 2008 R2 :
http://technet.microsoft.com/en-us/security/bulletin/ms11-030
PluginOutput :
SeeAlso :
CVE : CVE-2011-0657
BID : 47242
ExternaReference : {OSVDB:71780, IAVA:2011-A-0039, MSFT:MS11-030}
PatchPublicationDate : 2011/04/12
VulnPublicationDate : 2011/04/12
Exploitability : Exploits are available
ExploitAvailable : true
CANVAS :
Metasploit : true
COREImpact : true
MetasploitModule : Microsoft Windows DNSAPI.dll LLMNR Buffer Underrun DoS
CANVASPackage :
CVSSVector : CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C
CVSSBase : 10.0
CVSSTemporal : 7.8
PluginType : remote
PluginVersion :
Getting a Host KB and Plugin Audit
To get the KB is very simple and it is used mainly when opening support tickets with Tenable or when we want to trace what plugins executed or if we want to see what information some plugins used to determined if the host is vulnerable.
C:\> Get-NessusReportHostKB -Index 0 -ReportID a3fb5b8c-60db-1dda-fac7-ee46c0d0a638ea8ce79ab209483c -ReportHost 192.168.10.12 | Out-File -FilePath $env:HOMEPATH\Desktop\lab.txt
If we want to see the audit trail for a plugin that executed against a hosts we can retrieve it and it will tell us more information as to why it did not trigger:
C:\> Get-NessusReportPluginAudit 0 -ReportID a3fb5b8c-60db-1dda-fac7-ee46c0d0a638ea8ce79ab209483c -Host 192.168.10.12 -PluginID 35952 | fl Host : 192.168.10.12 PluginID : 35952 ExitCode : 1 Reason : Can't open socket on port 49777.
Conclusion
I hope you liked this short series. I’m currently working on expanding the functions for Nessus even more and looking forward to the new stuff that will be coming out with new releases so as to add support to those.